Welcome to the resource topic for 2021/1393
Title:
Fiat–Shamir Bulletproofs are Non-Malleable (in the Algebraic Group Model)
Authors: Chaya Ganesh, Claudio Orlandi, Mahak Pancholi, Akira Takahashi, Daniel Tschudi
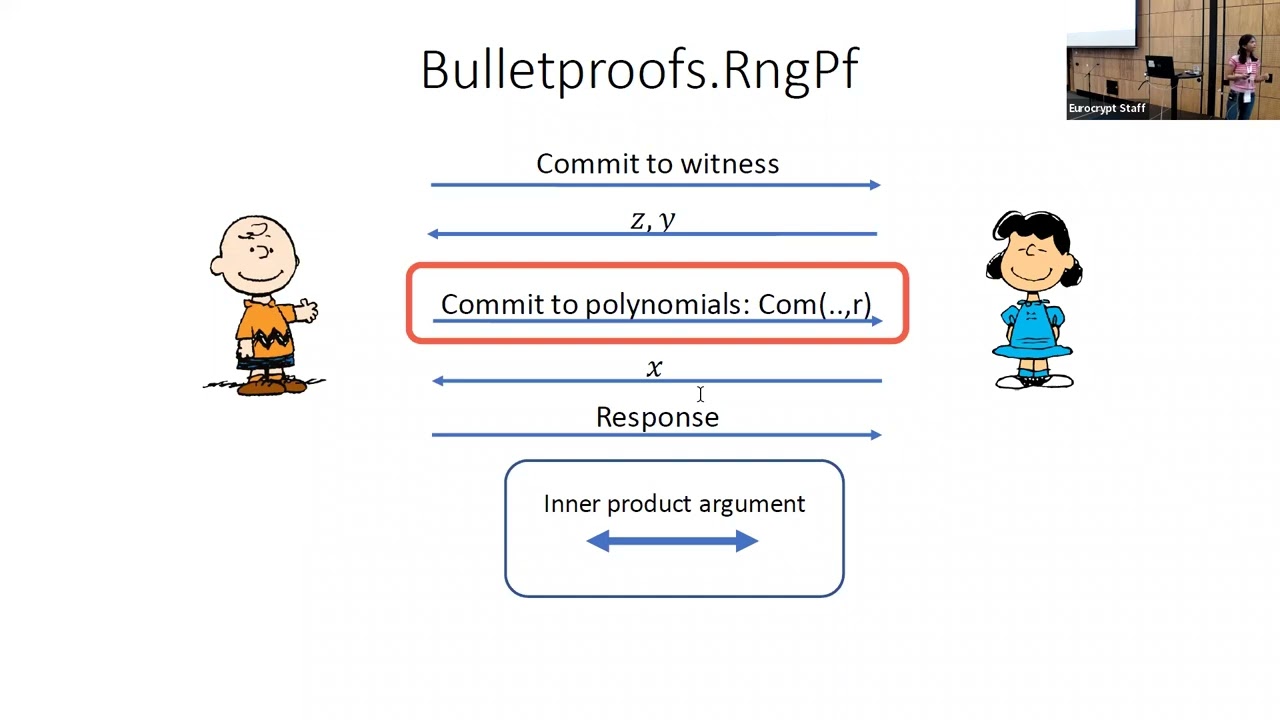
Abstract:Bulletproofs (Bünz et al. IEEE S&P 2018) are a celebrated ZK proof system that allows for short and efficient proofs, and have been implemented and deployed in several real-world systems. In practice, they are most often implemented in their non-interactive version obtained using the Fiat-Shamir transform, despite the lack of a formal proof of security for this setting. Prior to this work, there was no evidence that malleability attacks were not possible against Fiat-Shamir Bulletproofs. Malleability attacks can lead to very severe vulnerabilities, as they allow an adversary to forge proofs re-using or modifying parts of the proofs provided by the honest parties. In this paper, we show for the first time that Bulletproofs (or any other similar multi-round proof system satisfying some form of weak unique response property) achieve simulation-extractability in the algebraic group model. This implies that Fiat-Shamir Bulletproofs are non-malleable.
ePrint: https://eprint.iacr.org/2021/1393
Talk: https://www.youtube.com/watch?v=h3MhFkJ7I9s
Slides: https://iacr.org/submit/files/slides/2022/eurocrypt/eurocrypt2022/140/slides.pdf
See all topics related to this paper.
Feel free to post resources that are related to this paper below.
Example resources include: implementations, explanation materials, talks, slides, links to previous discussions on other websites.
For more information, see the rules for Resource Topics .