Welcome to the resource topic for 2020/900
Title:
Message-recovery Laser Fault Injection Attack on the Classic McEliece Cryptosystem
Authors: Pierre-Louis Cayrel, Brice Colombier, Vlad-Florin Dragoi, Alexandre Menu, Lilian Bossuet
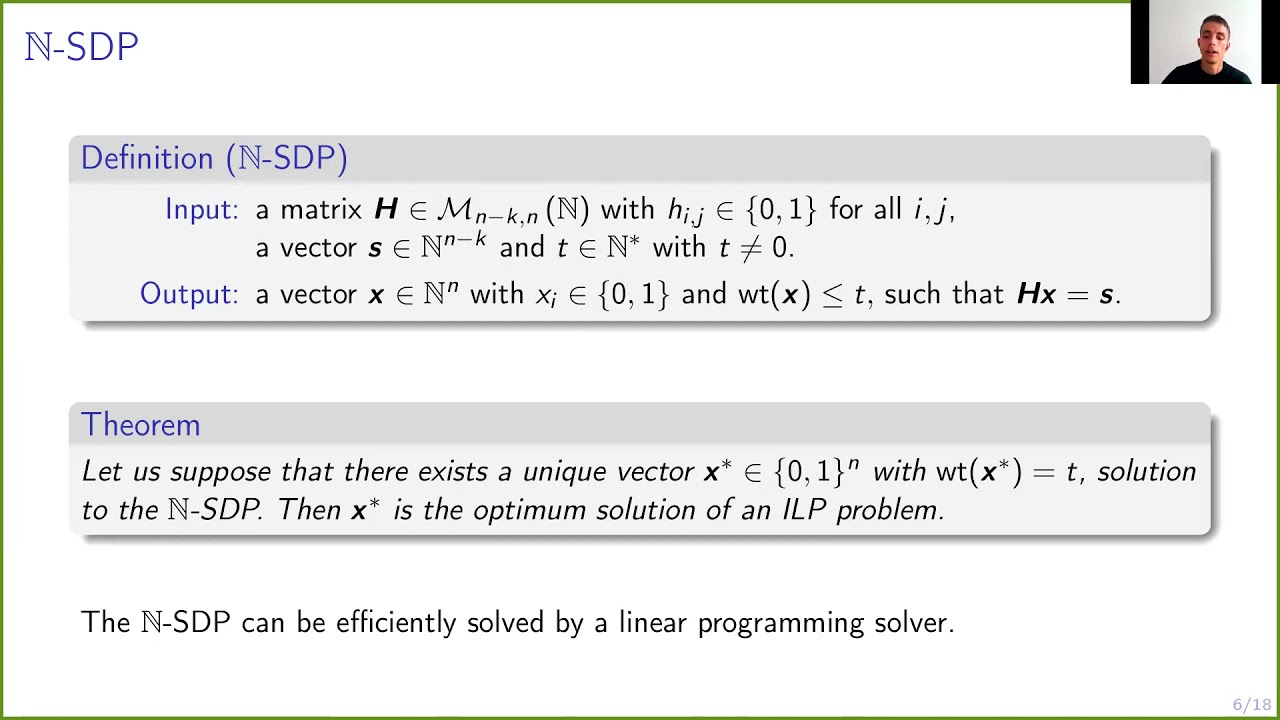
Abstract:Code-based public-key cryptosystems are promising candidates for standardization as quantum-resistant public-key cryptographic algorithms. Their security is based on the hardness of the syndrome decoding problem. Computing the syndrome in a finite field, usually \mathbb{F}_2, guarantees the security of the constructions. We show in this article that the problem becomes considerably easier to solve if the syndrome is computed in \mathbb{N} instead. By means of laser fault injection, we illustrate how to compute the matrix-vector product in \mathbb{N} by corrupting specific instructions, and validate it experimentally. To solve the syndrome decoding problem in \mathbb{N}, we propose a reduction to an integer linear programming problem. We leverage the computational efficiency of linear programming solvers to obtain real-time message recovery attacks against the code-based proposal to the NIST Post-Quantum Cryptography standardization challenge. We perform our attacks in the worst-case scenario, \textit{i.e.} considering random binary codes, and retrieve the initial message within minutes on a desktop computer. Our attack targets the reference implementation of the Niederreiter cryptosystem in the NIST PQC competition finalist \textit{Classic McEliece} and is practically feasible for all proposed parameters sets of this submission. For example, for the 256-bit security parameters sets, we successfully recover the message in a couple of seconds on a desktop computer. Finally, we highlight the fact that the attack is still possible if only a fraction of the syndrome entries are faulty. This makes the attack feasible even though the fault injection does not have perfect repeatability and reduces the computational complexity of the attack, making it even more practical overall.
ePrint: https://eprint.iacr.org/2020/900
Talk: https://www.youtube.com/watch?v=v0FsuXa7gXk
Slides: https://iacr.org/submit/files/slides/2021/eurocrypt/eurocrypt2021/154/slides.pdf
See all topics related to this paper.
Feel free to post resources that are related to this paper below.
Example resources include: implementations, explanation materials, talks, slides, links to previous discussions on other websites.
For more information, see the rules for Resource Topics .