Welcome to the resource topic for 2020/783
Title:
Adventures in Crypto Dark Matter: Attacks, Fixes for Weak Pseudorandom Functions
Authors: Jung Hee Cheon, Wonhee Cho, Jeong Han Kim, Jiseung Kim
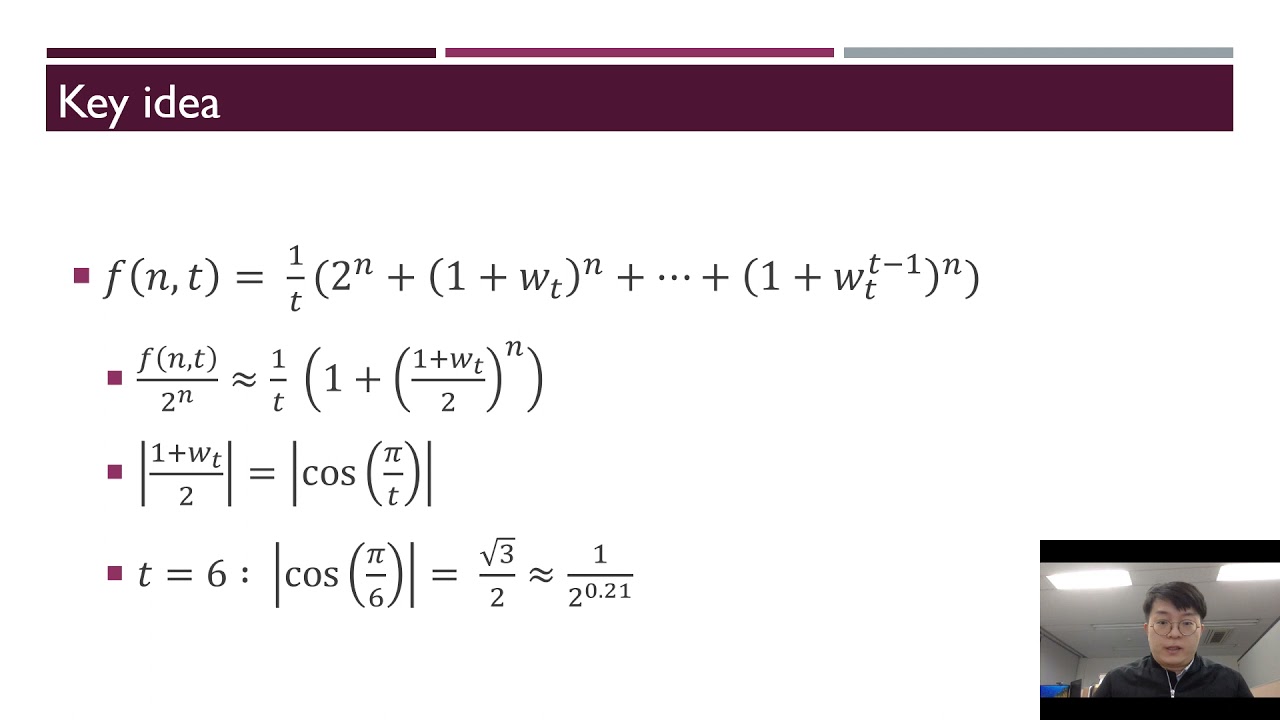
Abstract:A weak pseudorandom function (weak PRF) is one of the most important cryptographic primitives for its efficiency although it has lower security than a standard PRF. Recently, Boneh et al. (TCC’18) introduced two types of new weak PRF candidates, which are called a basic Mod-2/Mod-3 and alternative Mod-2/Mod-3 weak PRF. Both use the mixture of linear computations defined on different small moduli to satisfy conceptual simplicity, low complexity (depth-2 {\sf ACC^0}) and MPC friendliness. In fact, the new candidates are conjectured to be exponentially secure against any adversary that allows exponentially many samples, and a basic Mod-2/Mod-3 weak PRF is the only candidate that satisfies all features above. However, none of the direct attacks which focus on basic and alternative Mod-2/Mod-3 weak PRFs use their own structures. In this paper, we investigate weak PRFs from two perspectives; attacks, fixes. We first propose direct attacks for an alternative Mod-2/Mod-3 weak PRF and a basic Mod-2/Mod-3 weak PRF when a circulant matrix is used as a secret key. For an alternative Mod-2/Mod-3 weak PRF, we prove that the adversary’s advantage is at least 2^{-0.105n}, where n is the size of the input space of the weak PRF. Similarly, we show that the advantage of our heuristic attack to the weak PRF with a circulant matrix key is larger than 2^{-0.21n}, which is contrary to the previous expectation that `structured secret key’ does not affect the security of a weak PRF. Thus, for an optimistic parameter choice n = 2\lambda for the security parameter \lambda, parameters should be increased to preserve \lambda-bit security when an adversary obtains exponentially many samples. Next, we suggest a simple method for repairing two weak PRFs affected by our attack while preserving the parameters.
ePrint: https://eprint.iacr.org/2020/783
Talk: https://www.youtube.com/watch?v=yoHTfp706CQ
See all topics related to this paper.
Feel free to post resources that are related to this paper below.
Example resources include: implementations, explanation materials, talks, slides, links to previous discussions on other websites.
For more information, see the rules for Resource Topics .