Welcome to the resource topic for 2020/1076
Title:
Minimizing the Two-Round Tweakable Even-Mansour Cipher
Authors: Avijit Dutta
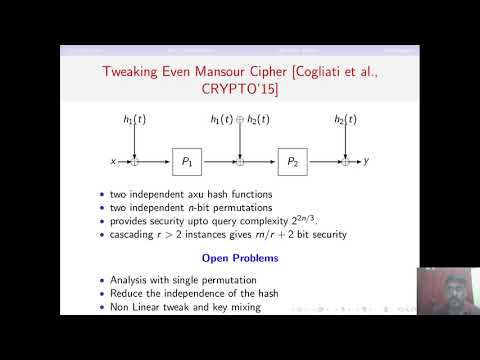
Abstract:In CRYPTO 2015, Cogliati et al. have proposed one-round tweakable Even-Mansour (\textsf{1-TEM}) cipher constructed out of a single n-bit public permutation \pi and a uniform and almost XOR-universal hash function \textsf{H} as (k, t, x) \mapsto \textsf{H}_k(t) \oplus \pi(\textsf{H}_k(t) \oplus x), where t is the tweak, and x is the n-bit message. Authors have shown that its two-round extension, which we refer to as \textsf{2-TEM}, obtained by cascading 2-independent instances of the construction gives 2n/3-bit security and r-round cascading gives rn/r+2-bit security. In ASIACRYPT 2015, Cogliati and Seurin have shown that four-round tweakable Even-Mansour cipher, which we refer to as \textsf{4-TEM}, constructed out of four independent n-bit permutations \pi_1, \pi_2, \pi_3, \pi_4 and two independent n-bit keys k_1, k_2, defined as $$k_1 \oplus t \oplus \pi_4(k_2 \oplus t \oplus \pi_3(k_1 \oplus t \oplus \pi_2(k_2 \oplus t \oplus \pi_1(k_1 \oplus t \oplus x)))),$$ is secure upto 2^{2n/3} adversarial queries. In this paper, we have shown that if we replace two independent permutations of \textsf{2-TEM} (Cogliati et al., CRYPTO 2015) with a single n-bit public permutation, then the resultant construction still guarrantees security upto 2^{2n/3} adversarial queries. Using the results derived therein, we also show that replacing the permutation (\pi_4, \pi_3) with (\pi_1, \pi_2) in the above equation preserves security upto 2^{2n/3} adversarial queries.
ePrint: https://eprint.iacr.org/2020/1076
Talk: https://www.youtube.com/watch?v=PAzVu5v3CR0
See all topics related to this paper.
Feel free to post resources that are related to this paper below.
Example resources include: implementations, explanation materials, talks, slides, links to previous discussions on other websites.
For more information, see the rules for Resource Topics .