Welcome to the resource topic for 2019/364
Title:
Everybody’s a Target: Scalability in Public-Key Encryption
Authors: Benedikt Auerbach, Federico Giacon, Eike Kiltz
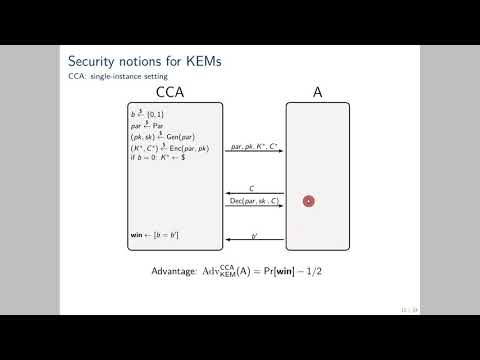
Abstract:For 1\leq m \leq n, we consider a natural m-out-of-n multi-instance scenario for a public-key encryption (PKE) scheme. An adversary, given n independent instances of PKE, wins if he breaks at least m out of the n instances. In this work, we are interested in the scaling factor of PKE schemes, \mathrm{SF}, which measures how well the difficulty of breaking m out of the n instances scales in m. That is, a scaling factor \mathrm{SF}=\ell indicates that breaking m out of n instances is at least \ell times more difficult than breaking one single instance. A PKE scheme with small scaling factor hence provides an ideal target for mass surveillance. In fact, the Logjam attack (CCS 2015) implicitly exploited, among other things, an almost constant scaling factor of ElGamal over finite fields (with shared group parameters). For Hashed ElGamal over elliptic curves, we use the generic group model to argue that the scaling factor depends on the scheme’s granularity. In low granularity, meaning each public key contains its independent group parameter, the scheme has optimal scaling factor \mathrm{SF}=m; In medium and high granularity, meaning all public keys share the same group parameter, the scheme still has a reasonable scaling factor \mathrm{SF}=\sqrt{m}. Our findings underline that instantiating ElGamal over elliptic curves should be preferred to finite fields in a multi-instance scenario. As our main technical contribution, we derive new generic-group lower bounds of \Omega(\sqrt{m p}) on the difficulty of solving both the m-out-of-n Gap Discrete Logarithm and the m-out-of-n Gap Computational Diffie-Hellman problem over groups of prime order p, extending a recent result by Yun (EUROCRYPT 2015). We establish the lower bound by studying the hardness of a related computational problem which we call the search-by-hypersurface problem.
ePrint: https://eprint.iacr.org/2019/364
Talk: https://www.youtube.com/watch?v=DWfXm9ANPPs
Slides: https://iacr.org/submit/files/slides/2020/eurocrypt/ec2020/289/slides.pdf
See all topics related to this paper.
Feel free to post resources that are related to this paper below.
Example resources include: implementations, explanation materials, talks, slides, links to previous discussions on other websites.
For more information, see the rules for Resource Topics .