Welcome to the resource topic for 2018/198
Title:
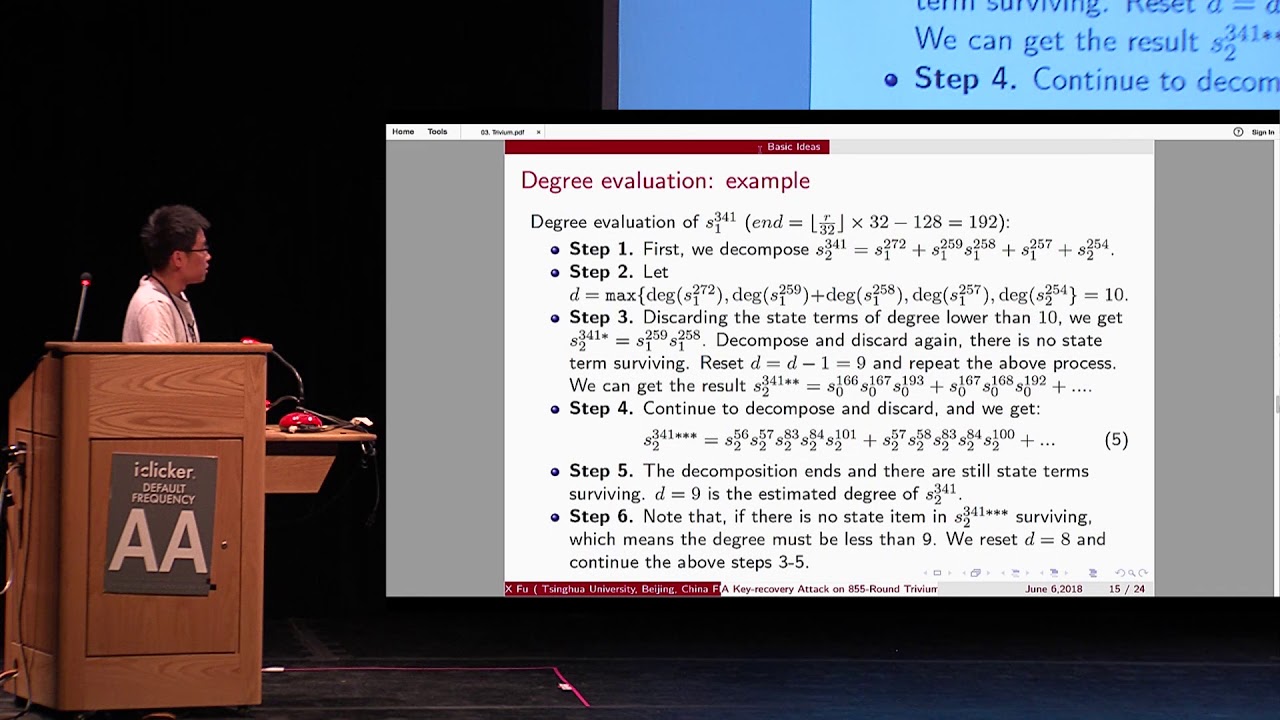
A Key-recovery Attack on 855-round Trivium
Authors: Ximing Fu, Xiaoyun Wang, Xiaoyang Dong, Willi Meier
Abstract:In this paper, we propose a key-recovery attack on Trivium reduced to 855 rounds. As the output is a complex Boolean polynomial over secret key and IV bits and it is hard to find the solution of the secret keys, we propose a novel nullification technique of the Boolean polynomial to reduce the output Boolean polynomial of 855-round Trivium. Then we determine the degree upper bound of the reduced nonlinear boolean polynomial and detect the right keys. These techniques can be applicable to most stream ciphers based on nonlinear feedback shift registers (NFSR). Our attack on 855-round Trivium costs time complexity 2^{77}. As far as we know, this is the best key-recovery attack on round-reduced Trivium. To verify our attack, we also give some experimental data on 721-round reduced Trivium.
ePrint: https://eprint.iacr.org/2018/198
Talk: https://www.youtube.com/watch?v=Fz3ZxA-H_98
Slides: https://crypto.iacr.org/2018/slides/A%20Key-recovery%20Attack%20on%20855-round%20Trivium.pdf
See all topics related to this paper.
Feel free to post resources that are related to this paper below.
Example resources include: implementations, explanation materials, talks, slides, links to previous discussions on other websites.
For more information, see the rules for Resource Topics .