Welcome to the resource topic for 2016/234
Title:
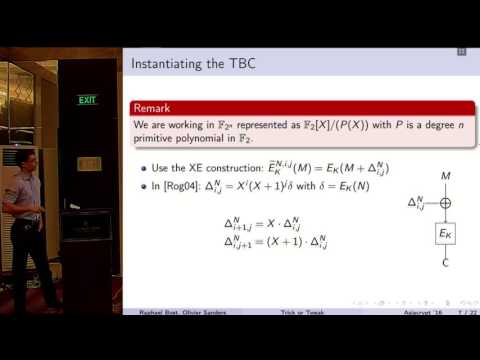
Trick or Tweak: On the (In)security of OTR’s Tweaks
Authors: Raphael Bost, Olivier Sanders
Abstract:Tweakable blockcipher (TBC) is a powerful tool to design authenticated encryption schemes as illustrated by Minematsu’s Offset Two Rounds (OTR) construction. It considers an additional input, called tweak, to a standard blockcipher which adds some variability to this primitive. More specifically, each tweak is expected to define a different, independent pseudo-random permutation. In this work we focus on OTR’s way to instantiate a TBC and show that it does not achieve such a property for a large amount of parameters. We indeed describe collisions between the input masks derived from the tweaks and explain how they result in practical attacks against this scheme, breaking privacy, authenticity, or both, using a single encryption query, with advantage at least 1/4. We stress however that our results do not invalidate the OTR construction as a whole but simply prove that the TBC’s input masks should be designed differently.
ePrint: https://eprint.iacr.org/2016/234
Talk: https://www.youtube.com/watch?v=MaByAJGfAFg
Slides: https://iacr.org/cryptodb/archive/2016/ASIACRYPT/presentation/27923.pdf
See all topics related to this paper.
Feel free to post resources that are related to this paper below.
Example resources include: implementations, explanation materials, talks, slides, links to previous discussions on other websites.
For more information, see the rules for Resource Topics .