Welcome to the resource topic for 2016/224
Title:
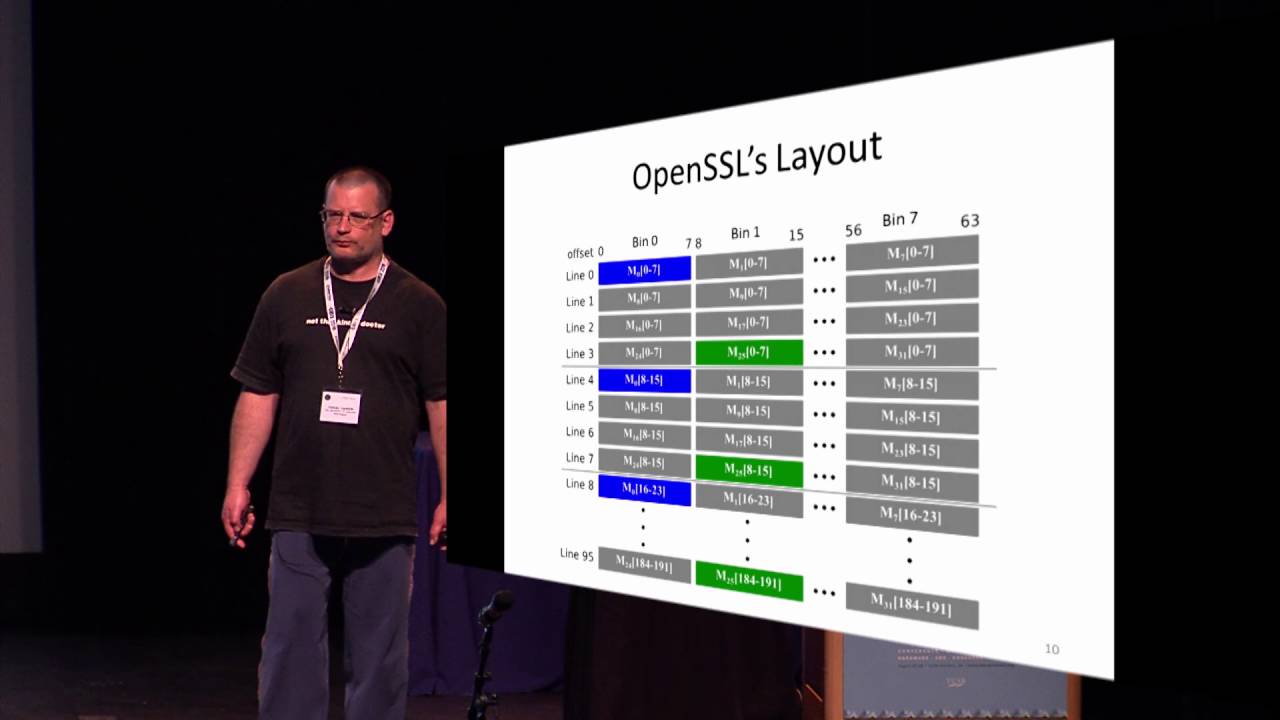
CacheBleed: A Timing Attack on OpenSSL Constant Time RSA
Authors: Yuval Yarom, Daniel Genkin, Nadia Heninger
Abstract:The scatter-gather technique is a commonly-implemented approach to prevent cache-based timing attacks. In this paper we show that scatter-gather is not constant-time. We implement a cache timing attack against the scatter-gather implementation used in the modular exponentiation routine in OpenSSL version 1.0.2f. Our attack exploits cache-bank conflicts on the Sandy Bridge microarchitecture. We have tested the attack on an Intel Xeon E5-2430 processor. For 4096-bit RSA our attack can fully recover the private key after observing 16,000 decryptions.
ePrint: https://eprint.iacr.org/2016/224
Talk: https://www.youtube.com/watch?v=Fjz4dkU2N3g
See all topics related to this paper.
Feel free to post resources that are related to this paper below.
Example resources include: implementations, explanation materials, talks, slides, links to previous discussions on other websites.
For more information, see the rules for Resource Topics .