Welcome to the resource topic for 2016/101
Title:
Signature Schemes with Efficient Protocols and Dynamic Group Signatures from Lattice Assumptions
Authors: Benoit Libert, San Ling, Fabrice Mouhartem, Khoa Nguyen, Huaxiong Wang
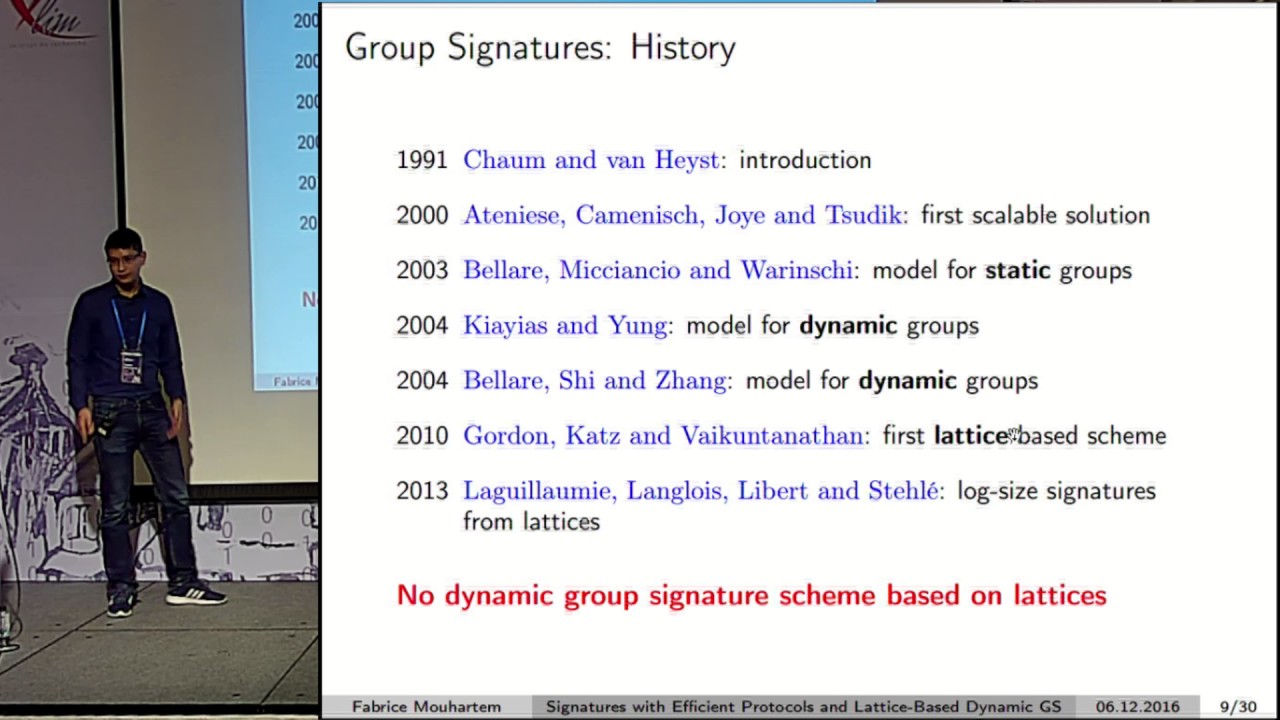
Abstract:A recent line of works - initiated by Gordon, Katz and Vaikuntanathan (Asiacrypt 2010) - gave lattice-based constructions allowing users to authenticate while remaining hidden in a crowd. Despite five years of efforts, known constructions are still limited to static sets of users, which cannot be dynamically updated. This work provides new tools enabling the design of anonymous authentication systems whereby new users can join the system at any time. Our first contribution is a signature scheme with efficient protocols, which allows users to obtain a signature on a committed value and subsequently prove knowledge of a signature on a committed message. This construction is well-suited to the design of anonymous credentials and group signatures. It indeed provides the first lattice-based group signature supporting dynamically growing populations of users. As a critical component of our group signature, we provide a simple joining mechanism of introducing new group members using our signature scheme. This technique is combined with zero-knowledge arguments allowing registered group members to prove knowledge of a secret short vector of which the corresponding public syndrome was certified by the group manager. These tools provide similar advantages to those of structure-preserving signatures in the realm of bilinear groups. Namely, they allow group members to generate their own public key without having to prove knowledge of the underlying secret key. This results in a two-message joining protocol supporting concurrent enrollments, which can be used in other settings such as group encryption. Our zero-knowledge arguments are presented in a unified framework where: (i) The involved statements reduce to arguing possession of a \{-1,0,1\}-vector \mathbf{x} with a particular structure and satisfying \mathbf{P}\cdot \mathbf{x} = \mathbf{v} \bmod q for some public matrix \mathbf{P} and vector \mathbf{v}; (ii) The reduced statements can be handled using permuting techniques for Stern-like protocols. Our framework can serve as a blueprint for proving many other relations in lattice-based cryptography.
ePrint: https://eprint.iacr.org/2016/101
Talk: https://www.youtube.com/watch?v=vF_z7mQjigg
Slides: https://iacr.org/cryptodb/archive/2016/ASIACRYPT/presentation/27858.pdf
See all topics related to this paper.
Feel free to post resources that are related to this paper below.
Example resources include: implementations, explanation materials, talks, slides, links to previous discussions on other websites.
For more information, see the rules for Resource Topics .