Welcome to the resource topic for 2014/961
Title:
When are Fuzzy Extractors Possible?
Authors: Benjamin Fuller, Leonid Reyzin, Adam Smith
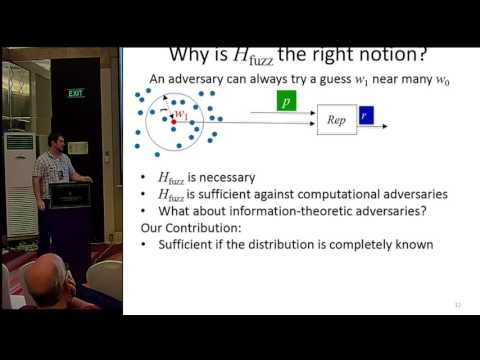
Abstract:Fuzzy extractors (Dodis et al., SIAM J. Computing 2008) convert repeated noisy readings of a high-entropy secret into the same uniformly distributed key. A minimum condition for the security of the key is the hardness of guessing a value that is similar to the secret, because the fuzzy extractor converts such a guess to the key. We codify this quantify this property in a new notion called fuzzy min-entropy. We ask: is fuzzy min-entropy sufficient to build fuzzy extractors? We provide two answers for different settings. 1) If the algorithms have precise knowledge of the probability distribution W that defines the noisy source is a sufficient condition for information-theoretic key extraction from W. 2) A more ambitious goal is to design a single extractor that works for all possible sources. This more ambitious goal is impossible: there is a family of sources with high fuzzy min-entropy for which no single fuzzy extractor is secure. This is true in three settings: a) for standard fuzzy extractors, b) for fuzzy extractors that are allowed to sometimes be wrong, c) and for secure sketches, which are the main ingredient of most fuzzy extractor constructions.
ePrint: https://eprint.iacr.org/2014/961
Talk: https://www.youtube.com/watch?v=xsijulzMqAc
Slides: https://iacr.org/cryptodb/archive/2016/ASIACRYPT/presentation/27924.pptx
See all topics related to this paper.
Feel free to post resources that are related to this paper below.
Example resources include: implementations, explanation materials, talks, slides, links to previous discussions on other websites.
For more information, see the rules for Resource Topics .