Welcome to the resource topic for 2013/424
Title:
Instantiating Random Oracles via UCEs
Authors: Mihir Bellare, Viet Tung Hoang, Sriram Keelveedhi
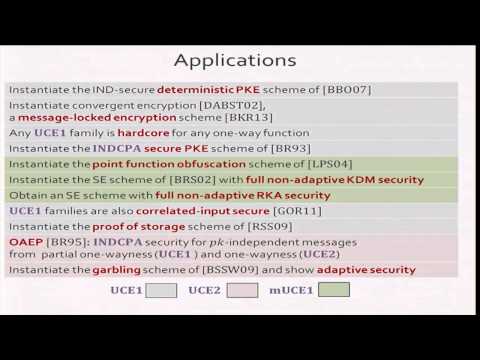
Abstract:This paper provides a (standard-model) notion of security for (keyed) hash functions, called UCE, that we show enables instantiation of random oracles (ROs) in a fairly broad and systematic way. Goals and schemes we consider include deterministic PKE, message-locked encryption, hardcore functions, point-function obfuscation, OAEP, encryption secure for key-dependent messages, encryption secure under related-key attack, proofs of storage and adaptively-secure garbled circuits with short tokens. We can take existing, natural and efficient ROM schemes and show that the instantiated scheme resulting from replacing the RO with a UCE function is secure in the standard model. In several cases this results in the first standard-model schemes for these goals. The definition of UCE-security itself asks that outputs of the function look random given some ``leakage,‘’ even if the adversary knows the key, as long as the leakage is appropriately restricted.
ePrint: https://eprint.iacr.org/2013/424
Talk: https://www.youtube.com/watch?v=ruYHFU4Jedc
See all topics related to this paper.
Feel free to post resources that are related to this paper below.
Example resources include: implementations, explanation materials, talks, slides, links to previous discussions on other websites.
For more information, see the rules for Resource Topics .